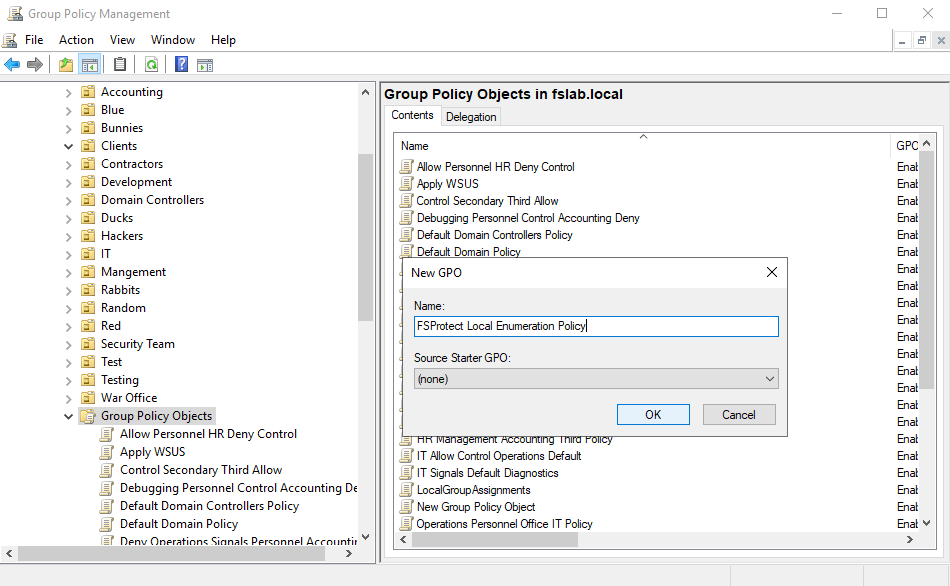
Creating new Group Policy Object
| Target Computers | Protocol | Protocol2 | Port | Description |
|---|---|---|---|---|
| DC or DNS Servers | TCP/UDP | DNS | 53 | To resolve names in AD environment with the help of DNS. |
| DC and CA Servers | TCP/UDP | HTTP | 80 | To perform Certificate Services related vulnerability checks. |
| DC Servers | TCP/UDP | KERBEROS | 88 | To authenticate in the domain with Kerberos. |
| DC or NTP Server | TCP/UDP | NTP | 123 | To resolve time in environment |
| DC Servers | TCP/UDP | LDAP | 389 | To collect the data with the help of LDAP queries. |
| DC and CA Servers | TCP/UDP | HTTPS | 443 | To perform Certificate Services related vulnerability checks. |
| DC Servers | TCP/UDP | LDAPS | 636 | To collect the data with the help of LDAP queries. |
| DC Servers | TCP/UDP | DCERPC | 49667 | To perform LSARPC queries |
| DC Servers | TCP/UDP | DCERPC | 49670 | To perform NETLOGON queries |
| DC Servers | TCP/UDP | DCERPC | All ports between 49152 – 65535 | To perform Spool Service related vulnerability checks. |
| All Computers in Domain | TCP/UDP | DCERPC | 135 | To collect local assets (Local Users, Local Groups, etc.) |
| All Computers in Domain | TCP/UDP | NETBIOS | 137 | To perform NETBIOS queries |
| All Computers in Domain | TCP/UDP | SMB | 445 | To perform SMB related vulnerability checks. |
| All Computers in Domain | TCP/UDP | RDP | 3389 | To perform RDP related vulnerability checks. |
| WSUS Servers | TCP | HTTP | 8530 | To perform WSUS related vulnerability checks. |
| WSUS Servers | TCP | HTTPS | 8531 | To perform WSUS related vulnerability checks. |
| Target Computers | Protocol | Protocol2 | Port | |
|---|---|---|---|---|
| FSProtect Deployed Server | TCP | HTTPS | 443 (Can be changed during installation) | Web App. UI |
| FSProtect Deployed Server | TCP | HTTPS | 8443 (Can be changed during installation) | REST API Access |
Creating new Group Policy Object
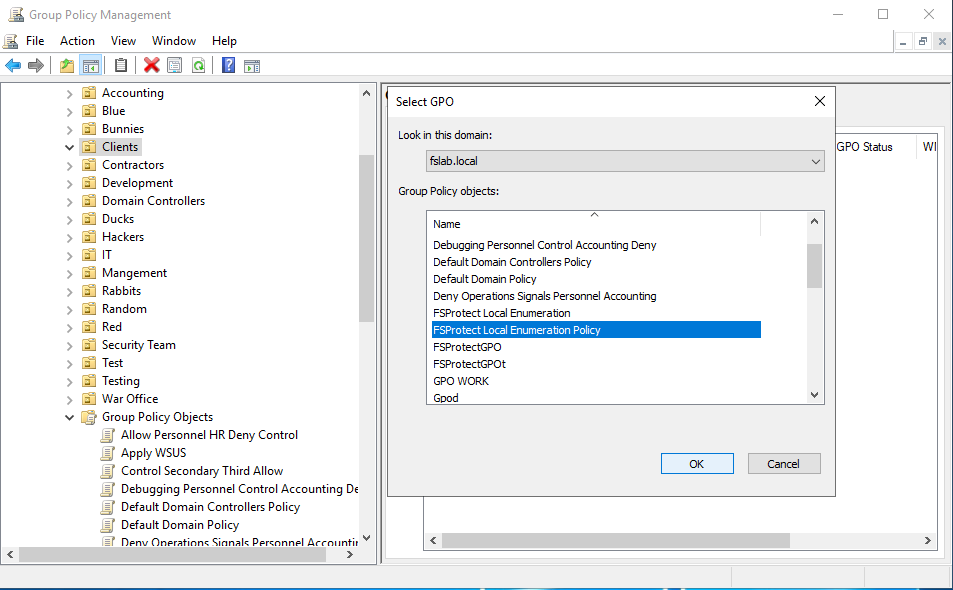
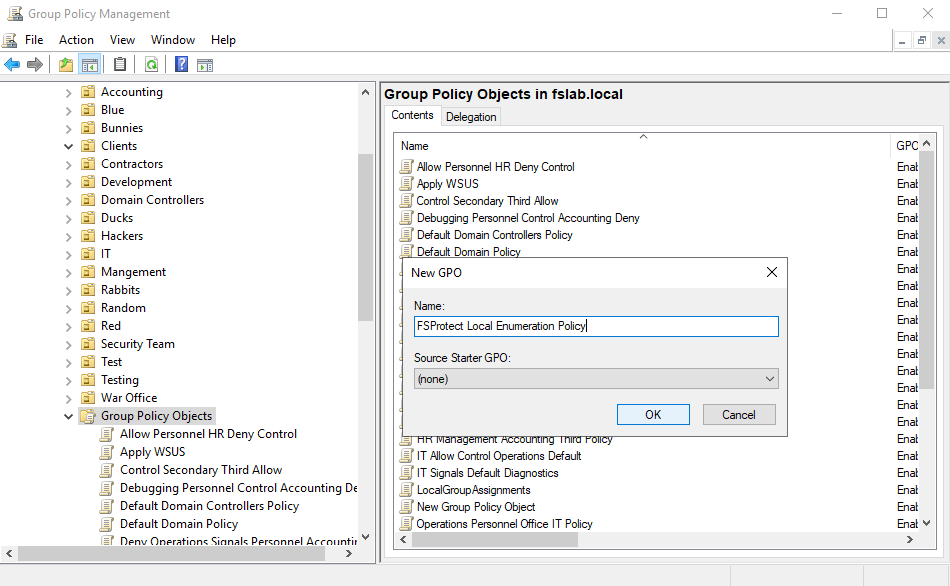
Linking a Group Policy Object to an Organizational Unit
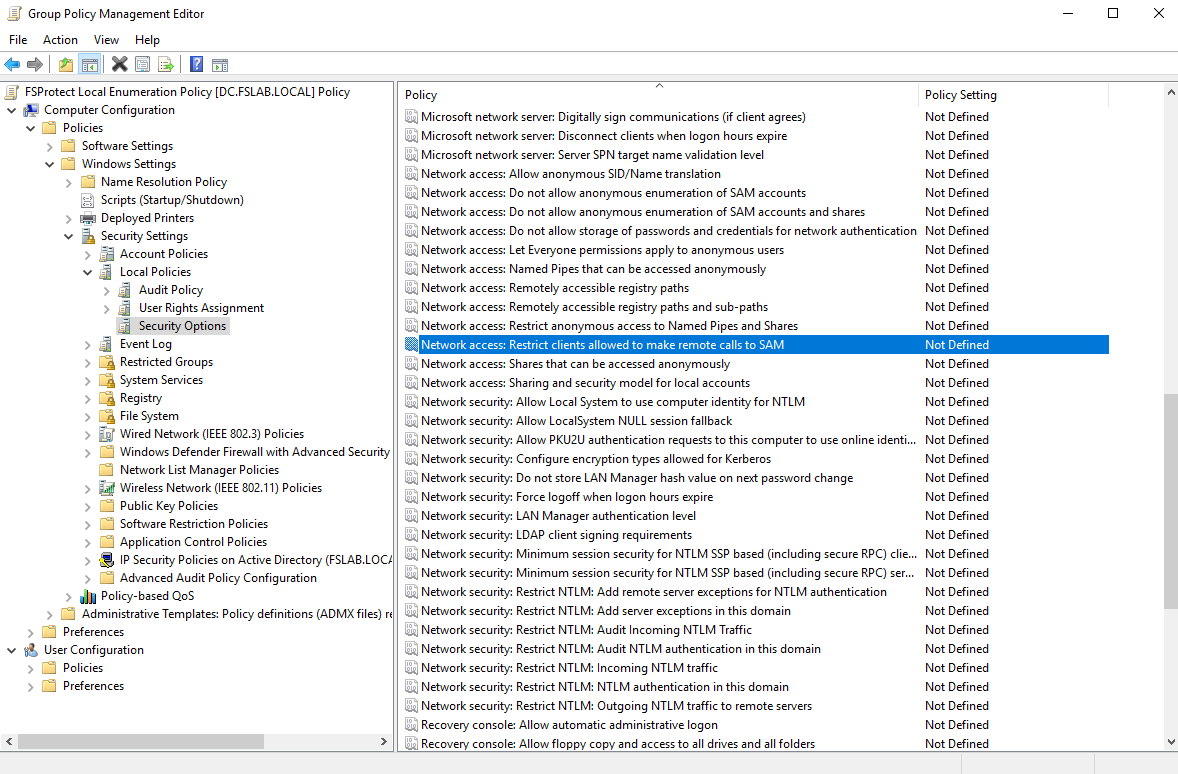
Navigating to the related Setting
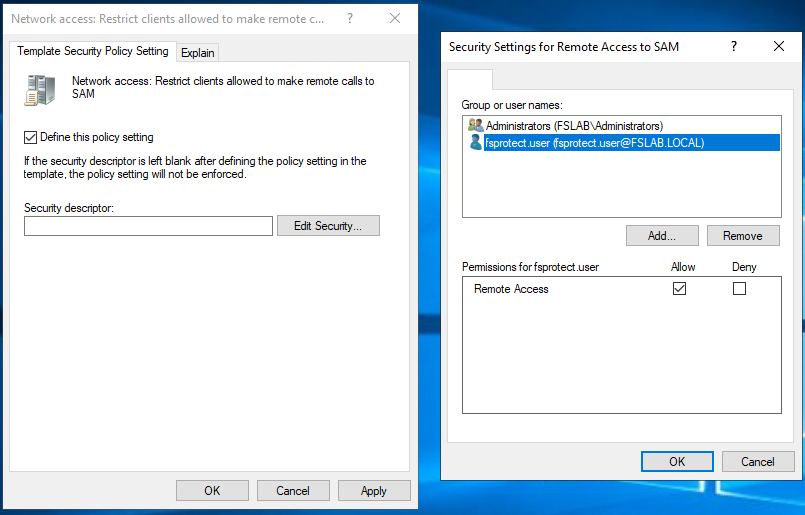
Granting Permission for FSProtect User
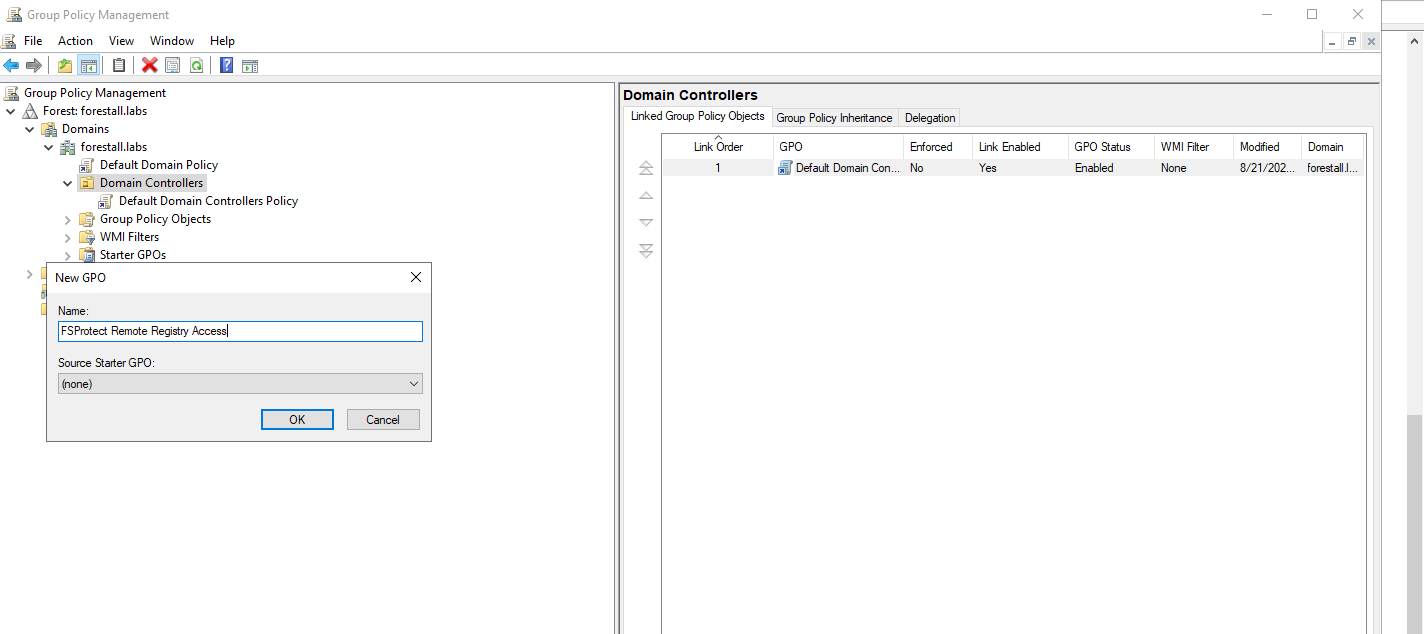
Creating new Group Policy Object
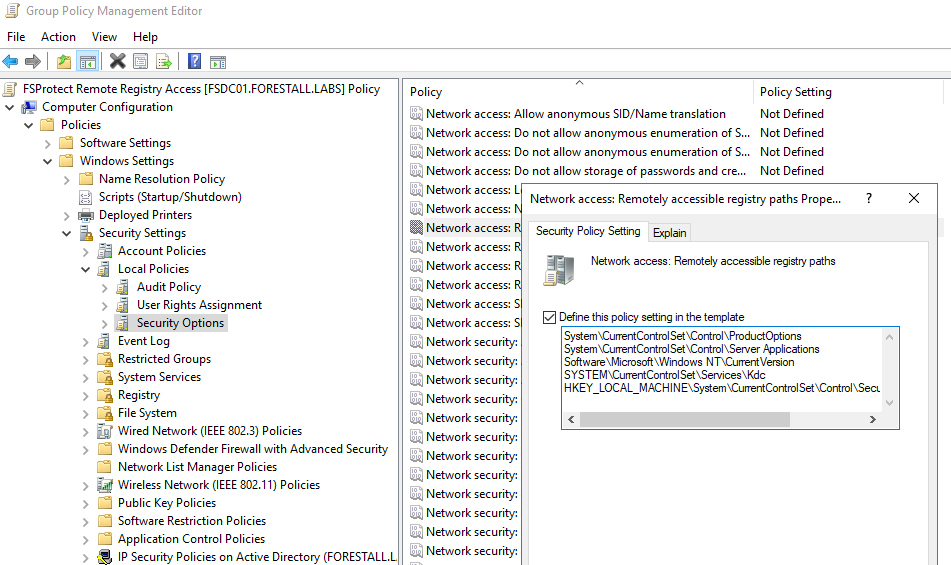
Granting Registry Read Permission for Domain Controllers
| No | Checklist Item | Status (Yes/No) |
|---|---|---|
| 1 | Has the server been set up according to the requirements specified for the installation of the FSProtect? (Requirement 1 and Requirement 2) | |
| 2 | Have the specified firewall rules been created for the network access? (Requirement 3 and Requirement 4) | |
| 3 | Can the server resolve all FQDNs and server IP addresses in Active Directory domains to be scanned? | |
| 4 | Are the security software on the server disabled or are necessary exclusions implemented? (Requirement 5) | |
| 5 | Is one of the Google Chrome, Mozilla Firefox or Microsoft Edge browsers installed on the server to access the FSProtect web interface? (Requirement 6) | |
| 6 | Have domain users with the specified requirements been created in all Forests to perform Active Directory scans? (Requirement 8) | |
| 7 | Has the required Group Policy object been created to perform local inventory enumeration? (Requirement 9) |